TL;DR
sudo rm -rf /* # can't have problems without a systemCopy. Paste. Enter.
Ok, this is a very good cheat sheet
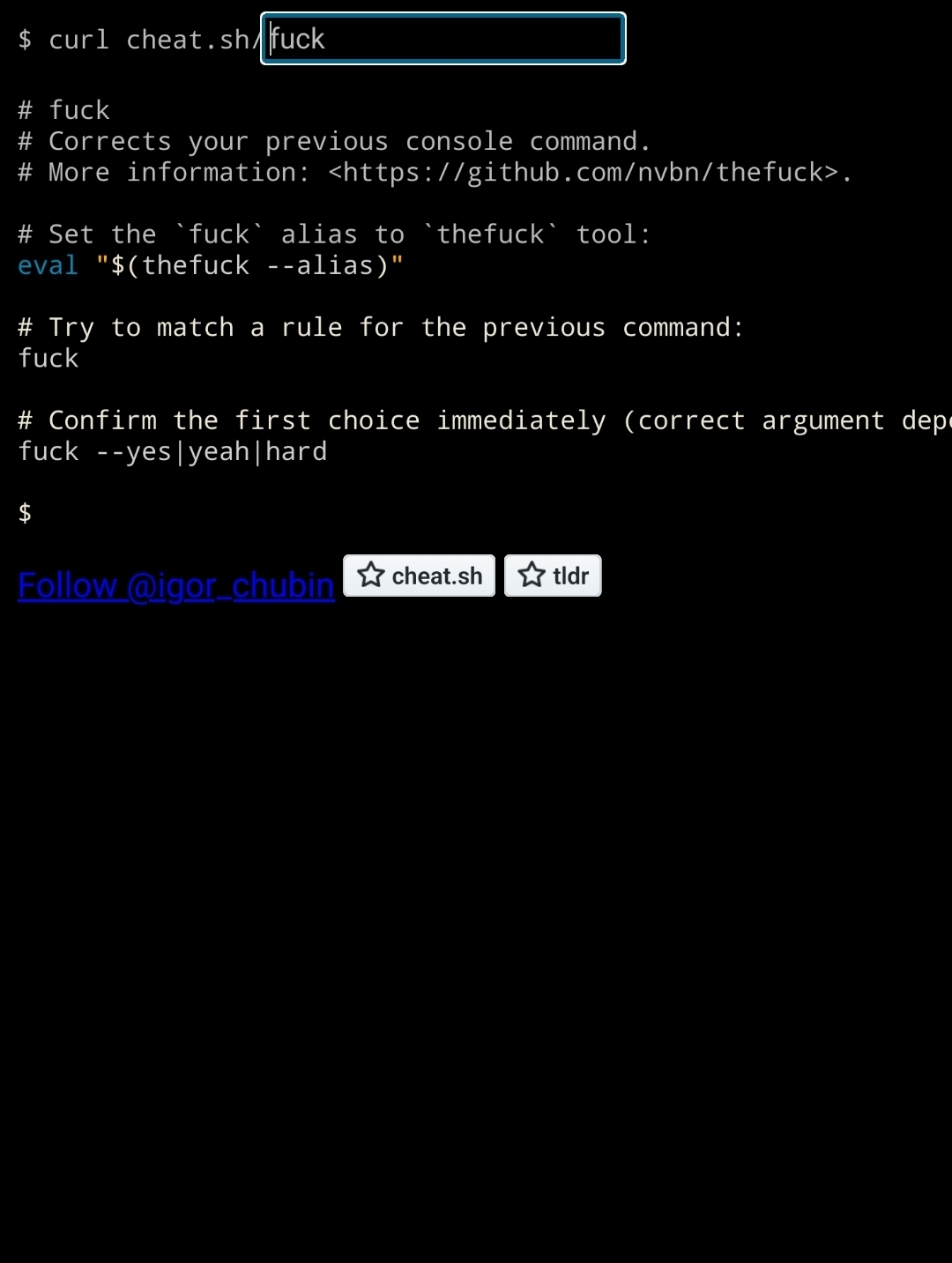
Thefuck is a cool program, but I stopped using it because it was slow.
I haven’t had as much luck with that program as I’d like to. :(
My
.bash_historyusing this program…
cheat() { curl cht.sh/$1 }Awesome!
sites like this are neat until you remember that curl’s willingness to write ansi escape codes to stdout when it is a tty (as this site relies on to format the output when the user agent is curl) is actually a security vulnerability.
Could you give me an ELI5 please
This post The Terminal Escapes: Engineering unexpected execution from command line interfaces has a summary of the longer paper in the first link.
tldr: There are a variety of ways that attackers can cause you to execute execute arbitrary code when you echo their maliciously-crafted data to your terminal. Therefore, when you run
curlwithout redirecting its output, or when youcata file you’ve downloaded, you’re trusting the server (and also the network, when you don’t havehttps://in the url) not to exploit you.Ah ok that makes sense, thank you!
I’m more-inclined to blame a virtual terminal than the program writing the sequences if there’s an exploit there.
Of course the terminal emulators are ultimately to blame but when there are so many problems in so many of them, imo curl’s default behavior should be to filter its output when writing to a tty.
is there a curl argument that can be used to block this behavior?
You can redirect curl’s output to a file with the
-o filenameoption (or with> filenamefor shell redirection). But in the case of sites like this which output ansi-escape-formatted data that isn’t very useful.Also, after saving unknown data to a file it’s common to look at it with
lessor perhapsxxdorstringsorfile… all of which have had their own CVEs in recent years 🤦Computer security is a fractal of bad news.
Appears to be the same developer as wttr.in
IIRC this site uses TLDR pages
deleted by creator