Could always plug it in temporarily; do what you gotta do, then remove it again.
🇨🇦
- 3 Posts
- 244 Comments
… Sata DVD-ROM drives are a thing
Hell I’ve still got one just in case

 26·9 days ago
26·9 days agoDrink less paranoia smoothie…
I’ve been self-hosting for almost a decade now; never bothered with any of the giants. Just a domain pointed at me, and an open port or two. Never had an issue.
Don’t expose anything you don’t share with others; monitor the things you do expose with tools like fail2ban. VPN into the LAN for access to everything else.
and using DDNS
As in, running software to update your DNS records automatically based on your current system IP. Great for dynamic IPs, or just moving location.
Sure, cloudflare provides other security benefits; but that’s not what OP was talking about. They just wanted/liked the plug+play aspect, which doesn’t need cloudflare.
Those ‘benefits’ are also really not necessary for the vast majority of self hosters. What are you hosting, from your home, that garners that kind of attention?
The only things I host from home are private services for myself or a very limited group; which, as far as ‘attacks’ goes, just gets the occasional script kiddy looking for exposed endpoints. Nothing that needs mitigation.

 251·9 days ago
251·9 days agoUnless you are behind CGNAT; you would have had the same plug+play experience by using your own router instead of the ISP supplied one, and using DDNS.
At least, I did.
It’s not immoral until you start having your kid throw games to swing the odds in your favor.
They just share a chimney. Extra Smokey flavor.

 73·15 days ago
73·15 days agoThe middle-man provides plausible deniability in this case. PornHub can genuinely say they don’t see connections from age-verification states atm. That stops being true if they host the VPN, making them aware of actual client locations.

 3·16 days ago
3·16 days ago‘connection refused’
But… I wanted to party… With some lemons…

 2·17 days ago
2·17 days agoAdam Savage exploring Makitas autonomous lawnmower R&D facility
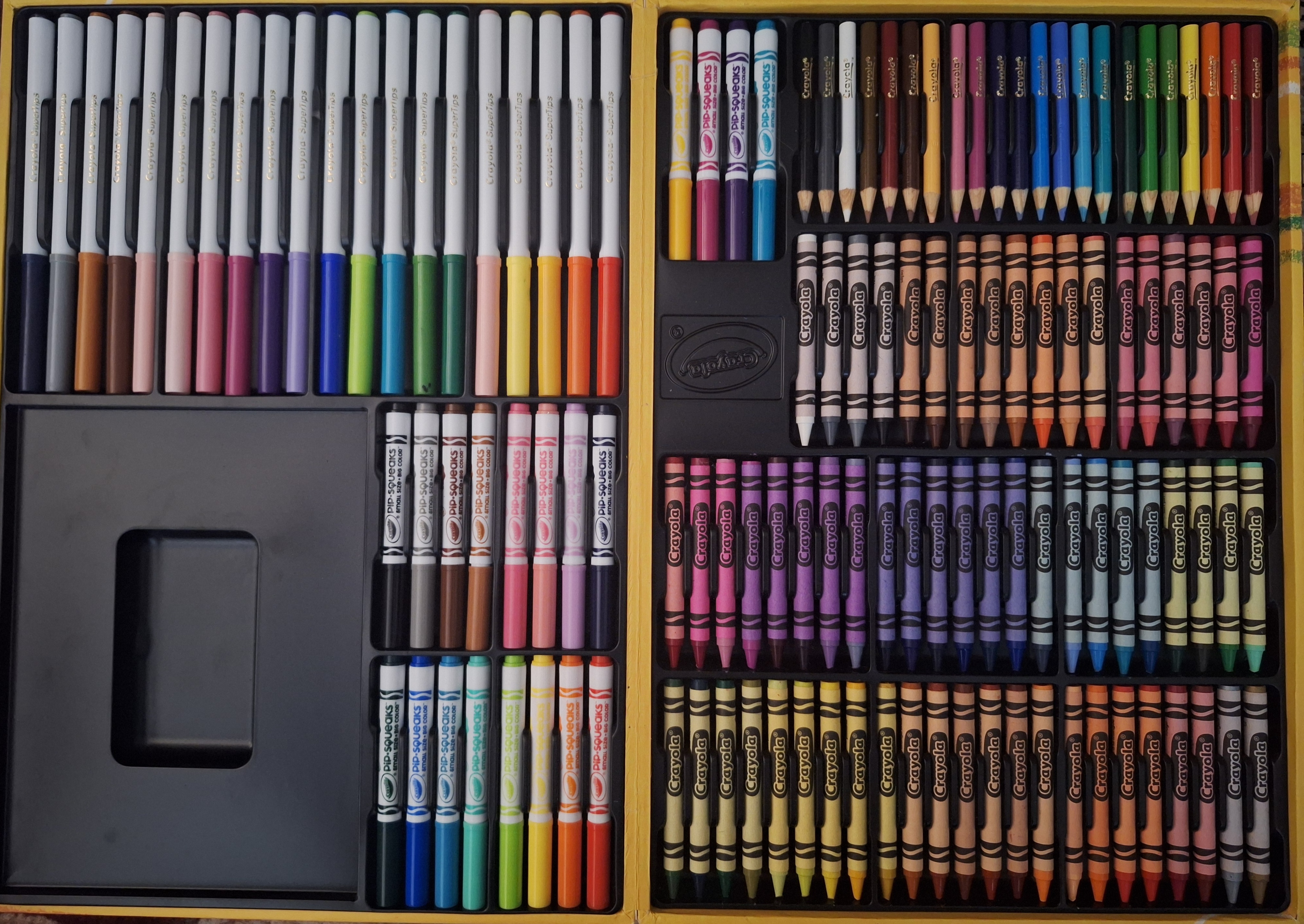
The smell when I open this thing is magnificent (it’s a briefcase)

 50·17 days ago
50·17 days agoThey’re often pretty quiet too.
Get an automatic/self-driving one, and you can just watch your vegetation be mutilated instead of doing it yourself.
I’m sure it just needs an oil change…
I’d just like to clarify: the new machines aren’t MRI (the magnets in those would prohibit all metal objects being within 100ft).
The new machines are also xray; but the xray emiters and detector are now on a spinning carriage similar to an MRI. This allows you to build a 3d model of the object and calculate it’s volume, which when combined with the density measurements gives much more reliable material detection.
This also means your stuff doesn’t have to be removed from bags to ensure items aren’t blocking each other from the scanner.
Fun fact: until recently, most airport scanners literally couldn’t differentiate between water and many common explosives. Hence the scrutiny of water based products/possessions.

 2·1 month ago
2·1 month agoI have one more thought for you:
If downtime is your concern, you could always use a mixed approach. Run a daily backup system like I described, somewhat haphazard with everything still running. Then once a month at 4am or whatever, perform a more comprehensive backup, looping through each docker project and shutting them down before running the backup and bringing it all online again.

 7·1 month ago
7·1 month agoI setup borg around 4 months ago using option 1. I’ve messed around with it a bit, restoring a few backups, and haven’t run into any issues with corrupt/broken databases.
I just used the example script provided by borg, but modified it to include my docker data, and write info to a log file instead of the console.
Daily at midnight, a new backup of around 427gb of data is taken. At the moment that takes 2-15min to complete, depending on how much data has changed since yesterday; though the initial backup was closer to 45min. Then old backups are trimmed; Backups <24hr old are kept, along with 7 dailys, 3 weeklys, and 6 monthlys. Anything outside that scope gets deleted.
With the compression and de-duplication process borg does; the 15 backups I have so far (5.75tb of data) currently take up 255.74gb of space. 10/10 would recommend on that aspect alone.
/edit, one note: I’m not backing up Docker volumes directly, though you could just fine. Anything I want backed up lives in a regular folder that’s then bind mounted to a docker container. (including things like paperless-ngxs databases)



127.0.0.1 is the loopback address. Ie it’s your computer trying to reach a service its hosting (prowlarr)/talk to itself. Sonarr/Radarr should be using this address as long as prowlarr+sonarr/radarr are on the same machine.
Prowlarr is either not running, or port 8080 is blocked by your firewall.